KickAss Torrents was once the most visited torrent index on the internet. After its 2016 shutdown, users have been navigating a patchwork of proxies, mirrors, and alternative platforms ever since. This guide explains how proxy access works, how to verify a proxy before trusting it, and what alternatives exist — with a clear breakdown of the tools involved and the failure modes you need to know about.
TL;DR
KAT shut down in 2016; proxy and mirror sites replicate its index but vary sharply in reliability and safety. To access them safely, pair a SOCKS5 proxy with a VPN and verify any domain before use. If proxies consistently fail, alternatives like 1337x or The Pirate Bay serve similar content. Check your local laws before downloading anything.
Legal note (quick)
Torrenting is a file-transfer technology — not inherently illegal. Legal uses include:
- Downloading Linux ISO distributions (Ubuntu, Fedora, and Debian all distribute official images via torrents)
- Accessing public domain films and books (the Internet Archive hosts thousands of legal, freely distributable torrents)
- Sharing Creative Commons-licensed music and software (many independent artists and developers release work under open licenses via torrent)
Whether accessing a KAT proxy is legal depends entirely on your country and on what you download. Some jurisdictions block torrent sites at the ISP level; others do not regulate access at all. Nothing in this guide constitutes legal advice. If you are uncertain about local law, consult a qualified attorney.
What was KickAss Torrents — and why did it disappear?
Founded around 2008, KickAss Torrents grew into one of the largest torrent indexes on the internet by the mid-2010s. It tracked tens of millions of torrents across movies, TV, software, music, and books. Unlike some competitors, it operated with a community-moderation model that kept content quality and organization unusually high.
In July 2016, the U.S. Department of Justice indicted Artem Vaulin, the alleged operator, on copyright infringement charges. The main domain was seized and the site went dark. What followed was a fragmented ecosystem: former moderators and third parties launched dozens of “mirror” and “proxy” sites carrying the KAT brand, with widely varying quality, safety records, and content freshness.
Understanding the distinction between a proxy and a mirror matters before you proceed:
Mirror site: An independently hosted copy of the original database, usually maintained by scraping or community contribution. The content is real but the host is unknown.
Proxy (reverse proxy): A server that sits between your browser and a destination, forwarding your request so your ISP sees only the proxy address. A proxy doesn’t necessarily host the content itself — it relays it.
In practice, most “KAT proxies” you’ll encounter today are mirrors with proxy-like domain structures — they host the torrent index directly rather than just forwarding requests.
How to find working KAT proxies safely
This is where most guides go wrong: they publish a list of domains and call it done. Domain lists go stale within weeks. A domain that resolved yesterday may redirect to a phishing page today, or serve malware through malicious ads.
Instead of a static list, here is a verification checklist you can apply to any domain you find — now or in the future.
Verification checklist
- HTTPS with a valid certificate — If your browser shows a certificate warning, close the tab immediately. No exceptions.
- Check domain registration age — Use a WHOIS lookup tool. A domain registered in the last 30 days claiming to be a longstanding “mirror” is a clear red flag.
- Compare content against known hashes — Real KAT mirrors carry authentic torrent hashes. Search for a well-known legal torrent (a Linux ISO works well). If results look fabricated or you’re immediately redirected to a download page, leave.
- No aggressive redirect chains — Legitimate mirrors don’t route you through three to five intermediate domains before showing content. If your browser tab flickers through multiple URLs, abort.
- Ad behavior check — Real-world mirror sites carry advertising, but legitimate ones don’t open new tabs unprompted or push browser notification requests. If a site does either, treat it as unsafe.
- Cross-reference with community sources — Torrent-focused forums and community boards often maintain crowd-verified lists. Prefer links discussed in threads with multiple replies over links from anonymous paste sites.
Examples to test
The following are domain formats commonly associated with KAT mirrors. These are examples only — status, safety, and content accuracy are not verified and may have changed. Apply the full checklist above before using any of them.
kickasstorrents.crkickass.sxkat.am
Disclaimer: Domain availability and safety change frequently. This list is illustrative, not a guarantee of functionality or trustworthiness.
Red flags checklist
- Domain created fewer than 60 days ago
- No HTTPS, or invalid/expired SSL certificate
- Immediate redirect to a third-party “download manager” installer
- Requests to disable browser security settings
- Login prompt asking for email and password (the original KAT never required login to browse)
- Torrent hashes that don’t match known-good copies of the same file
- Download links pointing to executable files rather than .torrent files or magnet links
Fallback steps if all proxies fail
- Switch to an established alternative (covered in the section below)
- Try Tor Browser — .onion versions of some mirrors exist and bypass ISP-level blocks entirely
- Change your DNS resolver to a public alternative (1.1.1.1 or 8.8.8.8) — ISP-level DNS blocking is the most common reason a valid domain won’t load
- Check whether your VPN provider offers split tunneling to route only browser traffic through the VPN
- Search current torrent community boards for freshly confirmed working domains — the community updates faster than any static article can
SOCKS5 proxy for torrenting: how the setup actually works
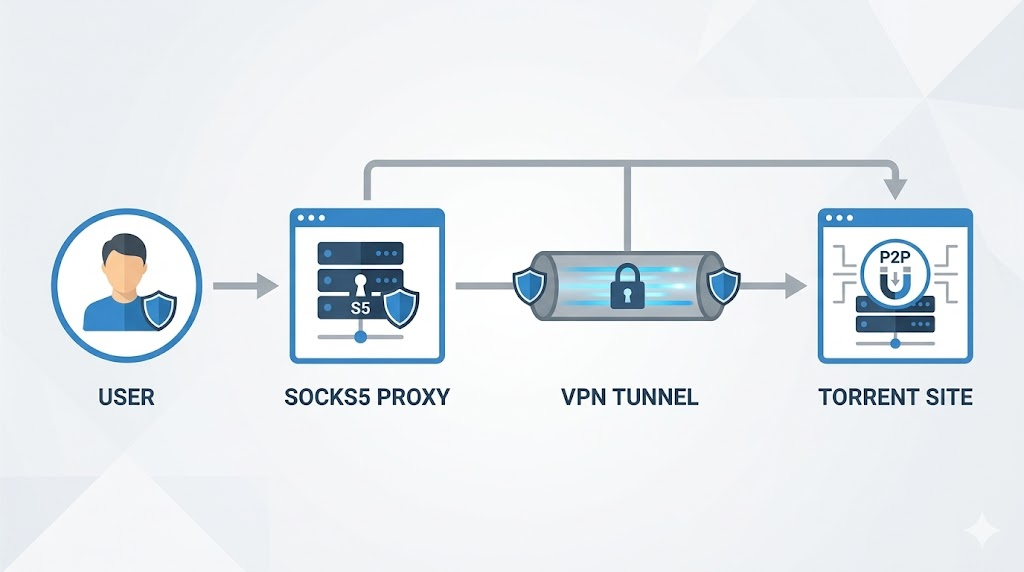
A SOCKS5 proxy is a general-purpose network proxy that operates at the socket level, meaning it handles both TCP and UDP traffic without modifying packet contents. For torrenting, this matters for several specific reasons:
- BitTorrent clients like qBittorrent and Deluge allow SOCKS5 configuration at the application level, routing only torrent traffic through the proxy while leaving your browser unaffected
- SOCKS5 supports UDP, which is required for DHT (Distributed Hash Table) — the peer-discovery mechanism that torrents rely on
- Unlike HTTP proxies, SOCKS5 doesn’t rewrite packet headers in ways that can inadvertently reveal your real IP address
However, SOCKS5 alone does not encrypt your traffic. Your ISP can still detect that you’re sending data to a proxy server — they just can’t easily see the destination. This is why combining SOCKS5 with a VPN addresses a different set of concerns than either tool alone.
Tradeoff table: VPN vs SOCKS5 proxy vs both
| Feature | VPN only | SOCKS5 only | VPN + SOCKS5 |
|---|---|---|---|
| Hides IP from torrent peers | Yes | Yes | Yes |
| Encrypts traffic from ISP | Yes | No | Yes |
| Torrent client-level granular control | No | Yes | Yes |
| Works with DHT / UDP | Depends on client | Yes | Yes |
| DNS leak protection | Depends on VPN | No | Depends on VPN |
| Speed overhead | Medium | Low | Medium–High |
| Kill switch support | Usually yes | Rarely | Depends on setup |
| Cost | Usually paid | Usually paid | Both costs apply |
| Setup complexity | Low | Medium | High |
The practical implication: if you only use a VPN, your torrent client may still send traffic outside the VPN tunnel in what’s called a “leak.” Configuring SOCKS5 at the client level closes that specific gap. Together, both tools address different layers of the same problem.
Configuring SOCKS5 in qBittorrent (general steps)
- Open qBittorrent → Tools → Options → Connection
- Under “Proxy Server”, select Type: SOCKS5
- Enter the proxy host address and port (provided by your proxy service)
- Check “Use proxy for peer connections”
- Enable “Disable connections not supported by proxies” — this prevents fallback to your real IP if the proxy is unavailable
- For combined setups: Tools → Options → Advanced → Network interface — bind to your VPN adapter
Where this breaks
SOCKS5 combined with a VPN is not foolproof. Specific failure points to know:
- WebRTC leaks in browsers — Browsers can expose your real IP through WebRTC even when a VPN is active. Disable WebRTC via a browser extension or verify at a public leak-check service.
- IPv6 leaks — Many VPNs protect IPv4 but not IPv6. If your ISP has assigned an IPv6 address and your VPN doesn’t tunnel it, peers in a torrent swarm can see it. Disable IPv6 in your OS network settings or choose a VPN with explicit IPv6 handling.
- DHT and PEX exposure — Even with a proxy, Distributed Hash Table and Peer Exchange can distribute your connection metadata. Disable both in your torrent client settings if anonymity is a priority.
- Proxy downtime mid-session — If your SOCKS5 proxy drops during an active session, some clients fall back to a direct connection. The “disable connections not supported by proxies” setting in qBittorrent is specifically designed to prevent this.
- Kill switch absent — If your VPN disconnects without a kill switch active, traffic continues unprotected. Verify your VPN has this feature enabled before relying on it.
- DNS not routed through proxy — If your torrent client resolves hostnames before the proxy handles them, your DNS queries still reveal browsing intent to your ISP. Use proxy-side DNS resolution if your client supports it.
- Client doesn’t support SOCKS5 over UDP — Older or misconfigured clients may not route UDP traffic through the proxy at all. Verify with a torrent IP checker — several free tools exist by searching “what is my torrent IP.”
Kickass torrent alternatives worth knowing
If KAT proxies prove consistently unreliable, the following platforms serve overlapping content and don’t require proxy access in most regions. Availability varies by country — some of these are also blocked in certain jurisdictions and have their own proxy ecosystems.
The Pirate Bay (TPB) — The longest-running major torrent index still operating. Older interface, active community, broad content range. Subject to ISP blocks in many countries, so proxy access follows similar logic to KAT.
1337x — Known for a cleaner interface and curated uploads. Particularly strong for movies, TV, and software. Has its own proxy ecosystem but is generally more stable than most KAT mirrors.
YTS (YIFY Torrents) — Focused exclusively on movies. Known for small, high-quality video encodes. Not suitable for software, music, books, or other categories.
RARBG — Shut down in May 2023 after 15 years of operation. Mirrors exist but serve a static archive (no new uploads). Useful for back-catalog content, not for current releases.
Nyaa.si — Specialized in anime and East Asian media. One of the most reliably maintained niche torrent indexes currently operating.
Internet Archive (archive.org) — For legal content specifically, the Archive hosts a large, torrent-accessible library of public domain films, books, audio recordings, and software. No proxy required; entirely above board.
How to choose a proxy provider
Not all proxy services are equal, and the wrong choice can expose rather than protect your traffic. These are the selection criteria that matter:
1. No-logs policy — A proxy provider that logs your activity provides no meaningful protection. Look for providers with published, independently audited no-logs policies — not just self-declared ones.
2. SOCKS5 support — HTTP proxies are insufficient for torrenting. Confirm SOCKS5 is explicitly supported and tested, not just listed somewhere in the feature set.
3. DNS leak prevention — Verify whether DNS queries are resolved server-side. Client-side DNS resolution through a proxy defeats much of its purpose, as your ISP still sees the destination hostnames.
4. Behavior on connection drop — Understand what happens when the proxy connection fails. Does your client fall back to a direct connection, or does it halt traffic entirely? The latter is what you want.
5. Provider jurisdiction — A company headquartered in a country with mandatory data retention laws is a structural risk regardless of its stated policies.
6. Server diversity — More geographic distribution generally means better latency options and fallback routes when a specific node is overloaded or blocked.
One option worth evaluating against these criteria is ColaProxy (ColaProxy.com), which offers SOCKS5 proxy access oriented toward users with privacy-focused torrenting use cases. Measure it against the criteria above the same way you would any provider — no service should be taken at face value without independent verification.
Key takeaways
- KAT shut down in 2016; proxies and mirrors fill the gap with inconsistent reliability and unknown operators behind them.
- Verify every proxy domain with HTTPS checks, WHOIS age lookups, and content hash comparison before trusting it.
- SOCKS5 proxy combined with VPN addresses both IP anonymity and traffic encryption, but each has specific documented failure modes.
- Alternatives like 1337x and YTS are more stable access points for most content categories available through KAT.
- Legal use cases for torrenting exist widely; your jurisdiction determines what is and isn’t permissible where you are.
Wrapping up
The KAT story is a useful lens for understanding how the broader torrent ecosystem operates: a platform goes down, a fragmented mirror landscape emerges, and users need a toolkit rather than a single URL to navigate it reliably. The tools covered here — SOCKS5 configuration, VPN kill switches, DNS leak checks, proxy verification checklists — are not KAT-specific. They apply across every torrent-adjacent context you’ll encounter.
Treat every new domain as untrusted until it clears the verification checklist. That habit protects you whether you’re looking for a KAT mirror or evaluating any other proxy-reliant service.
Frequently asked questions
Is KAT illegal?
It depends. Accessing a KAT proxy is not universally illegal — legality hinges on your country’s copyright and internet access laws, and on what you actually download. In some jurisdictions, visiting a blocked torrent site can carry legal risk; in others, there is no applicable law. Downloading copyrighted content without authorization is illegal in most countries. Using KAT or its mirrors to access legal content such as Linux ISOs or public domain files is generally unproblematic, but you should verify the law in your specific jurisdiction before proceeding.
Is KAT safe?
It depends on which domain you use and how you access it. The original KAT is gone, and current mirrors are operated by unknown third parties with no public accountability. Safety risks include malware embedded in torrent files, phishing through fake mirror domains, and data exposure over unprotected connections. Following a verification checklist, using a reputable SOCKS5 proxy and VPN, and scanning all downloads before opening them substantially reduces — but does not eliminate — these risks.
How do I access KAT if it’s blocked?
Yes, several methods work. The most practical are: (1) using a VPN that tunnels your connection through a server in an unblocked country, (2) configuring a SOCKS5 proxy in your torrent client or browser, (3) changing your DNS resolver to bypass ISP-level DNS blocking, or (4) accessing via Tor Browser for stronger anonymity. DNS changes alone often resolve simple ISP-level blocks without requiring a full VPN setup.
What are the best KAT alternatives?
It depends on your content category. For movies, YTS offers consistently high-quality encodes with a clean interface. For general content across categories, 1337x has reliable moderation and broad coverage. For archived older content, static RARBG mirrors remain searchable. For anime specifically, Nyaa.si is the strongest dedicated option. The Pirate Bay covers the broadest range but requires proxy access in many regions. No single platform fully replicates what KAT had at its peak.
Does a VPN hide torrenting?
Yes, from your ISP and network-level observers — a VPN encrypts traffic so your ISP sees only that you’re connected to a VPN server, not what content you’re transferring. However, a VPN does not protect against malware in downloaded files, does not prevent copyright holders from logging IP addresses visible in a torrent swarm (your VPN IP may still appear to peers), and does not guarantee anonymity if the VPN provider maintains logs and responds to legal requests.
