Proxy server types play a critical role in modern internet infrastructure, especially in web scraping, automation, cybersecurity, and data collection systems. In 2026, understanding different proxy server types is essential for building stable and scalable online operations.
As websites continue to strengthen anti-bot systems and IP filtering mechanisms, choosing the right proxy server types directly impacts success rate, stability, and performance. Understanding different proxy server types also helps optimize scalability and reduce detection risks.
This guide explains the main proxy server types, how they work, and how to choose the right one for different use cases.
Table of Contents
What is a Proxy Server and Proxy Server Types
A proxy server acts as an intermediary between a user and the internet. Instead of connecting directly to a website, requests are routed through a proxy, which forwards them on behalf of the user.
This process helps to:
- Hide the original IP address
- Improve anonymity and privacy
- Bypass geo-restrictions
- Distribute traffic across multiple IPs
- Reduce the risk of blocking or rate limiting
In modern automation systems, proxies are not just optional tools—they are part of the core infrastructure.
Why Proxy Types Matter in 2026
Modern websites no longer rely only on simple IP blocking. Instead, they analyze multiple signals such as:
- IP reputation and trust score
- Request frequency patterns
- Device fingerprinting
- Geographic consistency
- Session behavior
Because of this, using the wrong proxy type can lead to CAPTCHAs, throttling, or permanent bans.
Selecting the right proxy architecture is therefore critical for any scalable data operation.
Main Types of Proxy Servers

Residential Proxies
Residential proxies use IP addresses assigned by Internet Service Providers (ISPs) to real household devices. These IPs belong to real users, which makes them appear highly trustworthy to websites.
Because they mimic genuine user traffic, residential proxies are widely used in environments where detection risk is high.
They are especially effective for accessing platforms with strict anti-bot protection systems.
Residential proxies are commonly used in web scraping, market research, SEO tracking, and ad verification, where data accuracy and access stability are important.
Key advantages:
- Very high trust level from websites
- Low detection and blocking rate
- Strong compatibility with protected platforms
- Real-user traffic behavior
- Datacenter Proxies
Datacenter proxies are generated from cloud servers rather than real residential networks. They are designed for speed, scalability, and cost efficiency.
Because they originate from known server ranges, they are easier for websites to identify, especially on platforms with strong anti-bot protection.
However, they remain highly effective for large-scale operations where speed and volume are more important than stealth.
Datacenter proxies are widely used for bulk data collection, automation testing, and crawling open websites.
Key advantages:
- Extremely fast response time
- Cost-efficient at scale
- Easy to deploy in large quantities
- Stable performance under high load
ISP Proxies (Static Residential Proxies)
ISP proxies combine the stability of datacenter infrastructure with the trust level of residential IPs. They are hosted in data centers but registered with real ISPs, making them appear more legitimate.
This hybrid structure makes them ideal for tasks that require both consistency and reliability over long sessions.
They are often used in account-based operations where maintaining a stable identity is important.
Key advantages:
- Static and persistent IP addresses
- High connection stability
- Lower detection risk than datacenter proxies
- Suitable for login-based workflows
Mobile Proxies (4G/5G Proxies)
Mobile proxies route traffic through real mobile networks using 4G or 5G SIM cards. These IPs are assigned by mobile carriers and are shared among multiple users.
Because mobile IPs rotate naturally and represent real mobile traffic, they are extremely difficult for websites to block.
They are widely used in high-restriction environments where other proxy types fail.
Mobile proxies are particularly effective for social media platforms and sensitive automation tasks.
Key advantages:
- Highest anonymity level
- Extremely low detection probability
- Natural mobile network behavior
- Carrier-based dynamic IP rotation
Rotating Proxies
Rotating proxies automatically change the IP address after each request or within a defined time interval. This ensures that traffic is distributed across a large pool of IPs rather than coming from a single source.
This mechanism is especially useful for high-volume data collection systems that require continuous requests.
By rotating IPs, users can significantly reduce the risk of rate limits and bans.
Key advantages:
- Reduces IP blocking risk
- Supports high-concurrency scraping
- Distributes traffic across large IP pools
- Ideal for continuous crawling systems
SOCKS5 Proxies
SOCKS5 is a flexible proxy protocol that supports multiple types of internet traffic, including HTTP, HTTPS, and UDP.
Unlike standard HTTP proxies, SOCKS5 operates at a lower network level, allowing more versatile routing for different applications.
It is widely used in custom software systems and advanced automation setups.
Key advantages:
- Supports multiple protocols
- High flexibility for developers
- Stable low-level network routing
- Compatible with various applications
How to Choose the Right Proxy Type
For large-scale scraping or automation, choosing a reliable proxy provider is essential for long-term success.
Each proxy type serves a different purpose. The right choice depends on your use case:
- For high-trust environments and scraping → Residential proxies
- For speed and large-scale requests → Datacenter proxies
- For stable sessions and accounts → ISP proxies
- For maximum anonymity tasks → Mobile proxies
- For large-scale automation systems → Rotating proxies
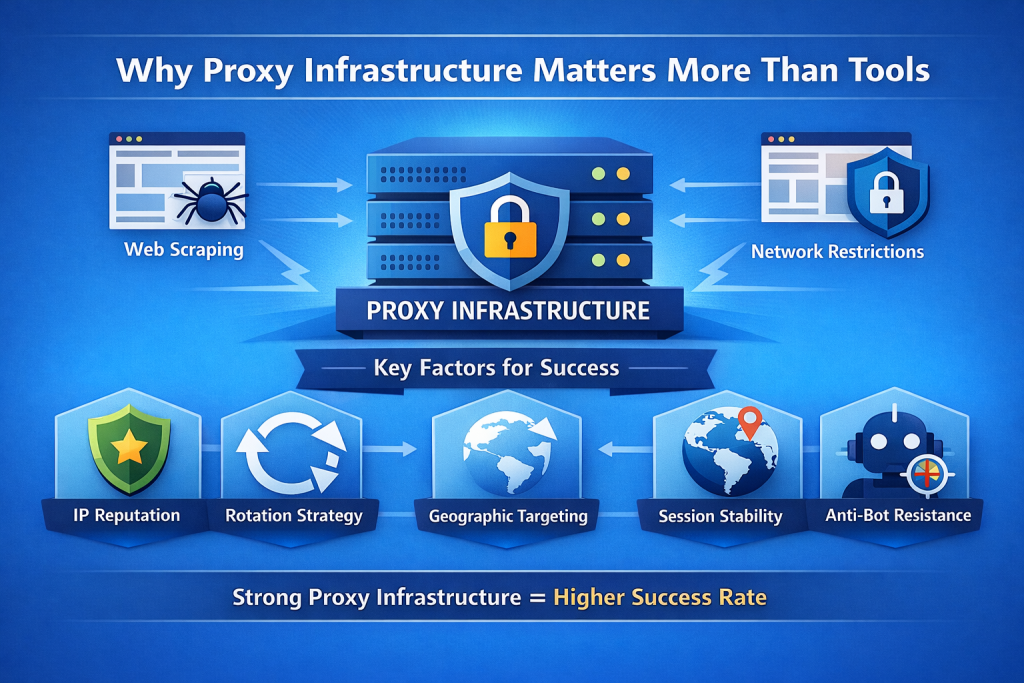
Why Proxy Infrastructure Matters More Than Tools
In real-world applications, most failures in scraping or automation are not caused by the software itself, but by network-level restrictions.
For a deeper understanding of how web scraping works, you can refer to this guide on web scraping.
Key factors that determine success include:
- IP reputation and trust level
- Rotation strategy efficiency
- Geographic alignment
- Session stability
- Anti-bot resistance
This is why modern systems rely heavily on strong proxy infrastructure rather than tools alone. rely heavily on strong proxy infrastructure rather than relying on a single tool.
ColaProxy for Scalable Proxy Infrastructure
ColaProxy provides a high-performance proxy infrastructure designed for modern data-driven applications.
It focuses on the core foundation of successful scraping systems:
- Large-scale residential proxy network
- High-quality ISP proxy pools
- Global geographic coverage
- High-concurrency stability
- Anti-detection optimized routing
Instead of replacing scraping tools, ColaProxy enhances them by improving success rates, stability, and scalability.
Conclusion
Understanding different proxy server types is essential for building reliable and scalable digital systems.
Each proxy type plays a specific role in modern infrastructure:
Residential proxies provide trust, datacenter proxies provide speed, ISP proxies ensure stability, mobile proxies offer maximum anonymity, and rotating proxies enable scale.
In 2026, proxy infrastructure is no longer optional—it is a core requirement for any serious data operation.
Businesses that choose the right proxy architecture gain a clear advantage in success rate, scalability, and long-term stability.
To learn more about proxy servers, you can check this explanation of proxy servers.