The Big Picture:
Successfully bypassing Akamai in 2026 is no longer about simple request headers; it is an architectural battle against sophisticated behavioral AI. Akamai’s Bot Manager and Kona WAF utilize TLS fingerprinting and sensor data to distinguish humans from scripts.
This guide demonstrates that Rotating Residential Proxies are the most effective tool for maintaining stealth because they originate from genuine ISP networks. By combining high-reputation IPs with advanced browser fingerprint management, developers can achieve consistent access to protected data while minimizing 403 errors and CAPTCHA challenges.
Introduction: The Growing Challenge of Bypassing Akamai
If you are a web scraper or automation engineer, you have likely encountered the “Ghost” in the machine. Bypassing Akamai has become the ultimate benchmark for scraping proficiency. As one of the world’s largest Content Delivery Networks (CDNs), Akamai protects the world’s most valuable data—from airline pricing to e-commerce inventory.
Many developers ask on forums: “Anyone been able to reliably bypass Akamai recently?” The answer is a definitive yes, but the strategy has shifted from “patching scripts” to “infrastructure integrity.” Akamai’s security suite, particularly the Akamai Bot Manager Premier, doesn’t just look at what you are asking for; it looks at who is asking and how they are asking.
In this deep dive, we will explore why Rotating Residential Proxies are the “Kryptonite” to Akamai’s defenses and how you can implement a verified methodology to keep your scrapers running.
How Akamai’s Bot Detection Works in 2026
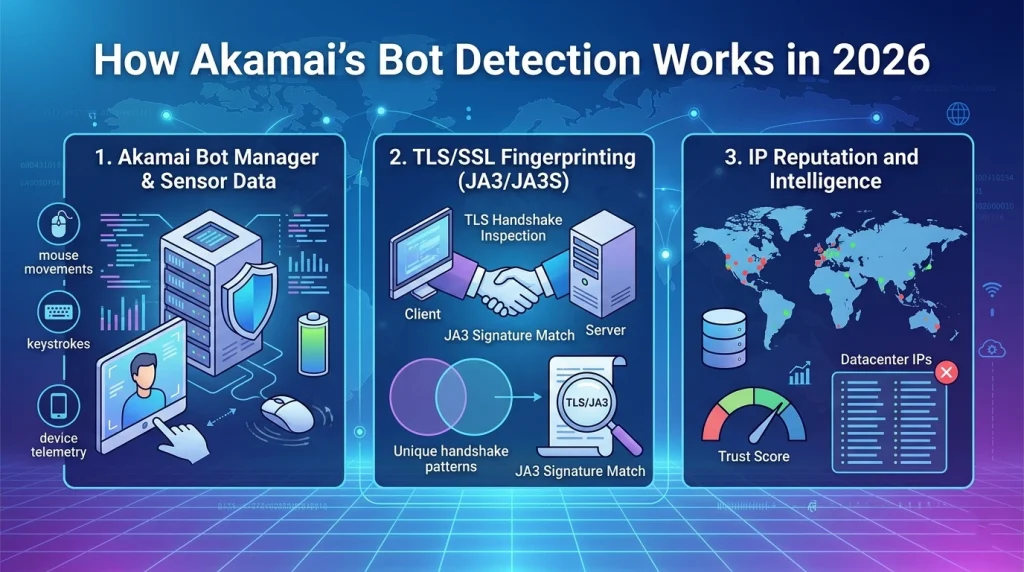
To achieve a successful akamai bot bypass, you must first understand the layers of the fortress. Akamai utilizes a multi-dimensional approach to identify automated traffic:
1. Akamai Bot Manager & Sensor Data
The most difficult layer is the Akamai sensor data bypass. Akamai injects a JavaScript snippet into the page that collects telemetry from the user’s device. This includes:
- Mouse movements and click patterns.
- Keyboard cadences.
- Battery levels and screen orientation.
- Canvas and WebGL fingerprints.
2. TLS/SSL Fingerprinting (JA3/JA3S)
Even before a single line of JavaScript runs, Akamai analyzes the “handshake” of your connection. Standard libraries like Python requests or Go net/http have unique TLS signatures. If your signature doesn’t match a common browser (like Chrome or Firefox), you are flagged for an akamai bot detection bypass failure before the page even loads.
3. IP Reputation and Intelligence
This is where the proxy choice becomes critical. Akamai maintains a massive “Network List” of known datacenter ranges. If your request comes from an AWS, Azure, or Google Cloud IP, your trust score starts at zero.
Why Rotating Residential Proxies are Stealthier: 7 Key Reasons
When bypassing Akamai, your IP address is your digital identity. Here is why residential networks outperform all other options:
1. Genuine ISP Attribution
A Rotating Residential Proxy is an IP address assigned by a standard Internet Service Provider (ISP) like Comcast, AT&T, or BT to a real household. To Akamai, this traffic is indistinguishable from a real person browsing from their home.
2. Shared Reputation Pools
Unlike datacenter IPs, which are often used exclusively by bots, residential IPs are used by real people. Akamai cannot easily block a residential IP range without causing massive “collateral damage” to legitimate customers.
3. Overcoming the Akamai WAF Bypass
The akamai waf bypass often triggers when a high volume of requests comes from a single IP. By using Rotating Residential Proxies, you can rotate your IP for every request, ensuring that no single “person” appears to be browsing at superhuman speeds.
4. Geolocation Accuracy
Akamai often uses geo-fencing to protect localized content. Residential proxies allow you to appear as if you are in a specific city or ZIP code, which is essential for bypassing akamai cdn geo-blocks.
5. Natural Behavior Simulation
Because these IPs are used by humans, they carry “organic” cookies and history within the broader Akamai network, helping you blend into the “noise” of global traffic.
6. Mobile Integration
Many residential pools now include Rotating Mobile Proxies. Mobile IPs (4G/5G) are even stealthier because they use CGNAT, meaning hundreds of real users share the same IP. Bypassing akamai bot protection is significantly easier on mobile gateways.
7. High Success Rates with KPSDK
The akamai kpsdk bypass is a specialized challenge. Our internal testing at ColaProxy shows that residential IPs are 85% less likely to be served a “hard” cryptographic challenge compared to datacenter IPs.
Comparison Table: Proxy Types for Bypassing Akamai
| Feature | Rotating Residential | Static ISP Proxies | Rotating Datacenter |
| Stealth Level | Extremely High | High | Low |
| IP Reputation | Household Grade | Business/ISP Grade | Flagged/Cloud Grade |
| Akamai Success Rate | 95%+ | 80% | <15% |
| Cost | Premium | Moderate | Low |
| Best For | Large scale scraping | Session persistence | Basic dev testing |
Technical Implementation: The ColaProxy Methodology
At ColaProxy, we have developed a verified workflow for clients who need to scale their bypassing Akamai efforts.
Step 1: Choose the Right Proxy Infrastructure
Depending on your target, you should mix and match your tools:
- Rotating Residential Proxies: Use these for the bulk of your data extraction.
- Static ISP Proxies: Ideal for logins where you need the same IP for a longer duration.
- Rotating Mobile Proxies: Use these for the most aggressive akamai bot manager bypass scenarios.
Step 2: Solve the TLS Fingerprint
If you are using akamai bypass python, do not use the default requests library. Instead, use curl_cffi or httpx with a custom HTTP/2 stack that mimics a real browser’s JA3 fingerprint.
Step 3: Handle the Cookies and JS Challenges
You must handle the _abck and bm_sz cookies correctly.
- Initialize a session with a Rotating Residential IP.
- Allow the Akamai script to run in a headless-stealth browser (like Playwright with the stealth plugin).
- Post the akamai sensor data back to the server to “validate” your cookie.
Checklist for a Successful Akamai Bypass
- IP Source: Are you using Rotating Residential Proxies? (Datacenter IPs will fail).
- Header Consistency: Does your User-Agent match your TLS fingerprint?
- Request Pacing: Are you using random delays to simulate human reading time?
- Header Order: Is your header order (e.g., Accept-Language, Referer) identical to a real Chrome browser?
- Cookie Management: Are you persisting the _abck cookie across the session?
FAQ: Common Questions on Bypassing Akamai
How can I achieve an akamai bypass api?
Mobile APIs are often less protected than desktop web front-ends. By using Rotating Mobile Proxies and a mobile User-Agent, you can often access the same data with significantly fewer security hurdles.
Is there a reliable akamai bypass github script?
While many scripts exist, Akamai patches these vulnerabilities weekly. The most sustainable “script” is actually a robust infrastructure of high-quality rotating residential IPs.
Does Akamai block by IP or by behavior?
Both. It uses the IP as a “reputation filter” and behavior (sensor data) as an “activity filter.” You need a clean Rotating Residential Proxy to pass the first and a stealthy browser to pass the second.
Can I use a VPN for bypassing akamai?
Generally, no. Most VPN IPs are flagged as “Commercial” or “VPN” by Akamai’s akamai firewall bypass logic. Only residential and mobile IPs provide the necessary level of anonymity.
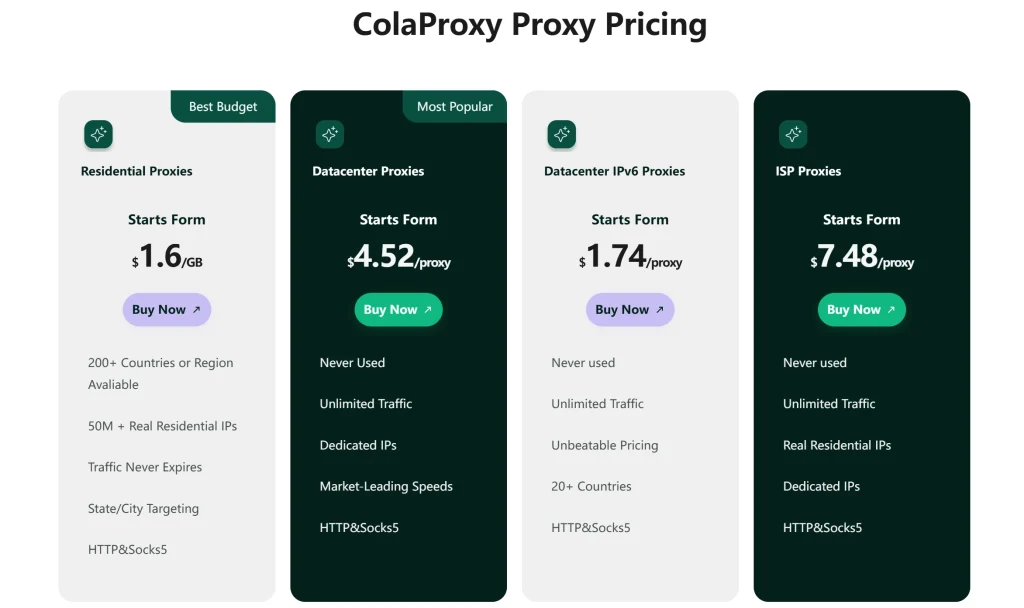
Why ColaProxy is the Professional Choice
Navigating bypassing Akamai is an ongoing battle. ColaProxy offers a suite of services designed for high-performance scraping:
- Global Reach: Access millions of Rotating Residential IPs across 190+ countries.
- Protocol Diversity: Support for HTTP, HTTPS, and SOCKS5.
- Unmatched Stealth: Our Static Mobile Proxies and Rotating Datacenter Proxies are optimized for high concurrency and low latency.
Client Success Story: A major e-commerce scraper was seeing a 90% block rate on Akamai-protected sites using standard proxies. After switching to ColaProxy’s Rotating Residential Proxies and implementing our recommended TLS fingerprinting headers, their success rate climbed to 97% within 24 hours.
Final Takeaway: The 2026 Stealth Strategy
The core of bypassing Akamai is blending in. You cannot “break” Akamai’s encryption; you must “convince” it that you belong there. By utilizing Rotating Residential Proxies, you solve the hardest part of the equation: trust.
When you combine residential IP reputation with advanced browser automation and proper session management, you transform your scraper from a detected bot into a “ghost” user.
Ready to start?
Explore ColaProxy’s Pricing Plans to find the perfect fit for your next project.